Falcon-512 produces the smallest digital signature of any algorithm currently approved by the US National Institute of Standards and Technology — and that fact quietly drove one of the bigger decisions in Solana’s recent development history.
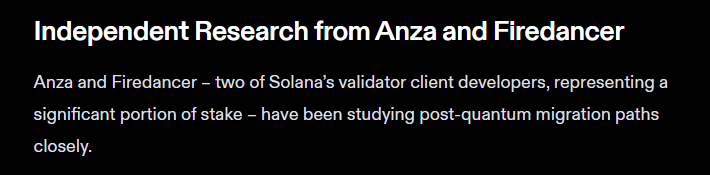
Two Teams, One Conclusion
Anza and Firedancer, two of Solana’s most widely used validator clients, have each rolled out a test version of Falcon, a post-quantum cryptographic signature scheme.
According to the teams, both groups researched the problem independently and landed on the same answer: quantum readiness is necessary, and Falcon is the right tool for the job.
Initial versions have been pushed to both clients’ GitHub repositories. Data from Anza’s account shows work on Falcon stretching back to at least January 27, 2026.
The solution is built to sit dormant until needed. It can be switched on if and when quantum computers grow powerful enough to crack public-key encryption — a hypothetical threshold researchers call Q-Day.
Source: Solana
Officials said the migration work is manageable, the transition can happen quickly when conditions demand it, and network performance is not expected to take a meaningful hit.
Why Signature Size Matters
For a high-throughput network like Solana, that last point is not a small thing. Post-quantum algorithms have generally been criticized for producing large signatures that strain bandwidth and storage — a direct threat to the kind of speed Solana is built around.
Source: Solana
Jump Crypto, the infrastructure firm behind Firedancer, said Falcon was chosen precisely because it avoids that problem. Signing happens offchain, and verification is not complex to implement.
Falcon is not the first quantum-resistant option to appear in Solana’s orbit. Blueshift’s Winternitz Vault has offered similar protections since January 2025, but it was designed as an optional add-on for individual users rather than a network-wide protocol upgrade. What Anza and Firedancer are doing sits at a different level entirely.
The Broader Pressure
Reports indicate that urgency around quantum threats has been building. Google and researchers at the California Institute of Technology said last month that functional quantum computers may arrive sooner than previously expected and could require far less computing power to break encryption than earlier estimates suggested.
Google went further, claiming quantum machines could potentially crack Bitcoin’s cryptography within 10 minutes.
Not everyone shares that alarm. Blockstream CEO Adam Back has described today’s quantum computers as lab experiments and argues no genuine threat will surface for decades.
Scott Aaronson, a leading researcher in quantum computing theory, generally agrees with Back, that quantum computers are not close to breaking systems like Bitcoin.
Aaronson argues that today’s machines are still far from the scale needed for real cryptographic threats, even if long-term preparation remains important.
Featured image from Unsplash, chart from TradingView

Editorial Process for bitcoinist is centered on delivering thoroughly researched, accurate, and unbiased content. We uphold strict sourcing standards, and each page undergoes diligent review by our team of top technology experts and seasoned editors. This process ensures the integrity, relevance, and value of our content for our readers.